Download the Citrix Workspace App
Citrix Workspace app is the easy-to-install client software that provides seamless secure access to everything you need to get work done.
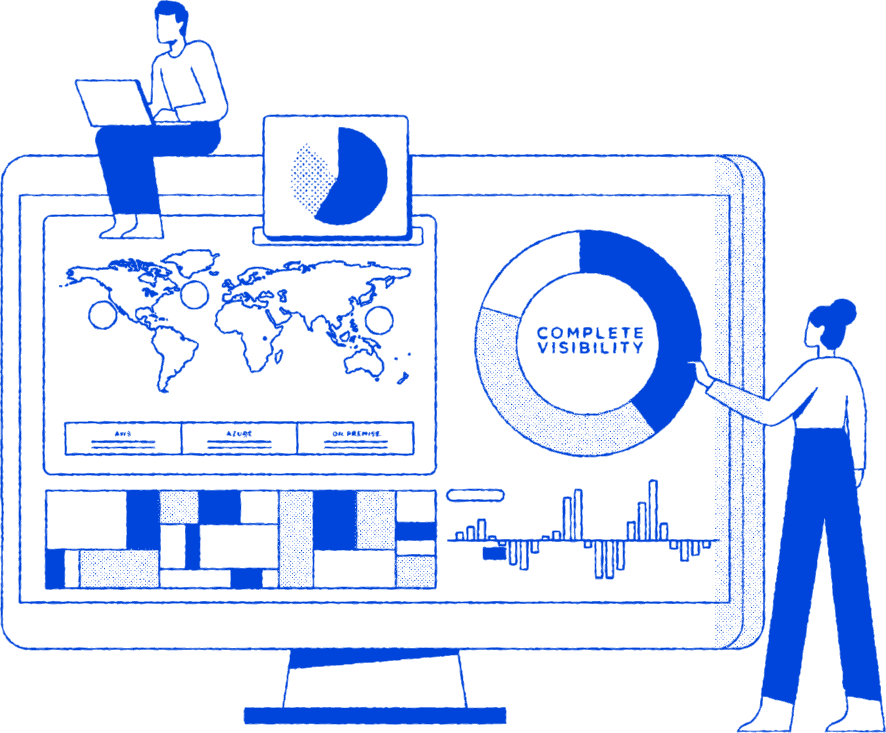
From virtualization and networking to ZTNA and security, you need a comprehensive infrastructure to successfully enable your employees. The Citrix® platform delivers everything you need to securely enable high-performance access to enterprise applications. The Citrix platform is a complete offering with virtual apps and desktops, Zero Trust access, and high-performance secure application delivery, all with end-to-end observability.
Leveraging the Citrix platform enables global enterprises to simplify complex, multi-vendor environments, maximize value and focus on the skill sets needed for successful application delivery infrastructure.
With the Citrix platform, you can deliver, monitor, and manage secure access to enterprise content to any user on any device. The Citrix platform is a comprehensive, enterprise-wide solution, which includes unparalleled Citrix and NetScaler® capabilities.
of the Fortune 100*
*Based on 2024 US Fortune 100 data
of internet users go through a NetScaler every day
improve time to resolve outages by 67% with Citrix observability
Deploy resources in any location that works best for your business - whether it’s on-premises or in public cloud. With our world-class flexibility, you can deploy in Azure, AWS, Google Cloud, or any number of hypervisor platforms. Manage them all seamlessly side-by-side with a unified management plane. Deliver an exceptional user experience no matter where or how your users access the environment with our flagship HDX technology.
Protect internet-facing and internal applications via NetScaler technology with granular security controls to grant and restrict access. With industry-leading one-pass architecture, NetScaler can perform many functions simultaneously to reduce latency and improve performance. Deliver applications globally and at scale with auto-scaling and global load balancing to ensure top of the line performance.
Replace your antiquated VPN with ZTNA. Implement ZTNA with adaptive access to all IT-sanctioned apps—web, SaaS, and client-server—whether they’re deployed on premises or in the cloud. Citrix solutions are built for the enterprise by isolating web browsing to securing web and SaaS apps. Provide secure least privilege access via secure Enterprise Browser with single sign-on and a unified portal to all work apps.
Empower IT to manage and grant context-aware and action-oriented secure application access. Offer device freedom to your end users to maximize user productivity and mobility to get their work done from anywhere. Enable employees while keeping sensitive data off unauthorized devices and keeping it secure with controls based on user context, like role, location, or device.
Streamline monitoring and troubleshooting across complex and hybrid Citrix landscapes and help improve your security posture with actionable data and security policies. With Citrix observability capabilities, you can also enhance user experience while decreasing service costs and boost support efficiency - all while reducing time to resolution and improving troubleshooting accuracy.
XenServer is the only hypervisor platform optimized for the Citrix platform. With seamless feature integration at every level, XenServer leverages hardware-level functionalities to deliver a high-definition user experience, enhanced security, and streamlined operational management.
Protect your business data against cybersecurity threats with end-to-end Zero Trust security.
Support distributed workforces by centralizing management and delivering apps to any device.
Deliver any resource to any device with the best user experiences.
Elevate the user experience when delivering virtual apps and desktops, even over challenging networks.
Hear from Calvin Hsu, Vice President of Product Marketing as he shares the latest Citrix updates, including the new Citrix Platform licensing, and other exciting plans for 2024.

Learn from experts, gain insight from fellow users, and contribute to knowledge on Citrix technologies and integrations for more successful Citrix deployments.