Download the Citrix Workspace App
Citrix Workspace app is the easy-to-install client software that provides seamless secure access to everything you need to get work done.
Workspace security refers to the application of tools and solutions to protect sensitive data, networks, and access in digital workspaces without disrupting the user experience.
Currently, there are many online options to deliver employees the applications, documents, and resources they need to perform their tasks from anywhere. Yet there are security concerns for remote working. A secure workspace solution can address employee expectations of a responsive experience while keeping sensitive information under tight security.
Explore additional worksapce security topics:
Workspace security ensures that workforces can function from anywhere at any time without compromising the organization’s security. The more solution providers, systems, and data connecting to an organization, the greater the security risks.
Here are two of the most pressing reasons to ensure your workspace remains secure:
Remote Work Is Here to Stay. After the COVID-19 pandemic, workers did not return to the office as quickly as expected and many businesses began moving to flexible schedules. These transitions to a hybrid workforce resulted in an increased attack surface as employees began to access company resources from more locations and on more devices.
While some companies provide managed laptops and tablets, they are not in the majority. Many companies encourage the use of personal devices through BYOD (bring your own device) programs to reduce costs. But how can an organization ensure the employees’ personal devices comply with their security standards, policies, and practices? A secure digital workspace that can be used safely from anywhere must separate the personal and professional environments of the employee.
Digital transformation requires a modern security stack. Companies undergoing digital transformation need to integrate new cloud environments with legacy datacenter infrastructure. Thus, the cloud security stack is becoming more complex to use and manage, and often includes too many security tools. There is a need for security solutions that can protect the entire threat surface, including application-level threats.
Companies face many data security risks when it comes to threat detection and prevention. For example:
Protecting an extended and disparate threat surface with siloed tools is ineffective. A decentralized security solution has gaps and cannot cover the entire threat surface, especially when the company grows and needs to scale operations. It takes time to configure and manage the stack of different tools, which can prevent a quick response to a potential attack.
A lack of data protection against attacks at the API level is concerning. On-premises security solutions have limited scalability, so they cannot protect against large-scale attacks. For instance, a volumetric DDoS attack can overwhelm an on-premises solution that may not stop it before it enters the network.
The castle and moat approach of cybersecurity is not effective against new threats, since now there is no “inside the castle.” This approach assumes that inside the “walls,” the risks are controlled and a user may conduct any activity they want. Many companies following this approach will add an appliance solution in the form of a VPN. However, an attacker who can get in (or is already inside) may find the weak spot, steal data, and get out before anyone realizes what is happening.
Many companies have their applications in the cloud but use on-premises threat prevention and data loss protection (DLP) tools. This increases the risk of stalling network traffic until the DLP tool can inspect and clear it through the network. This creates latency and produces a poor user experience.
ANALYST REPORT
IT security teams now need to manage a large and disparate attack surface while at the same time preventing internal threats. Users accessing cloud applications and business resources from various locations present a risk that cannot be addressed with the castle and moat approach.
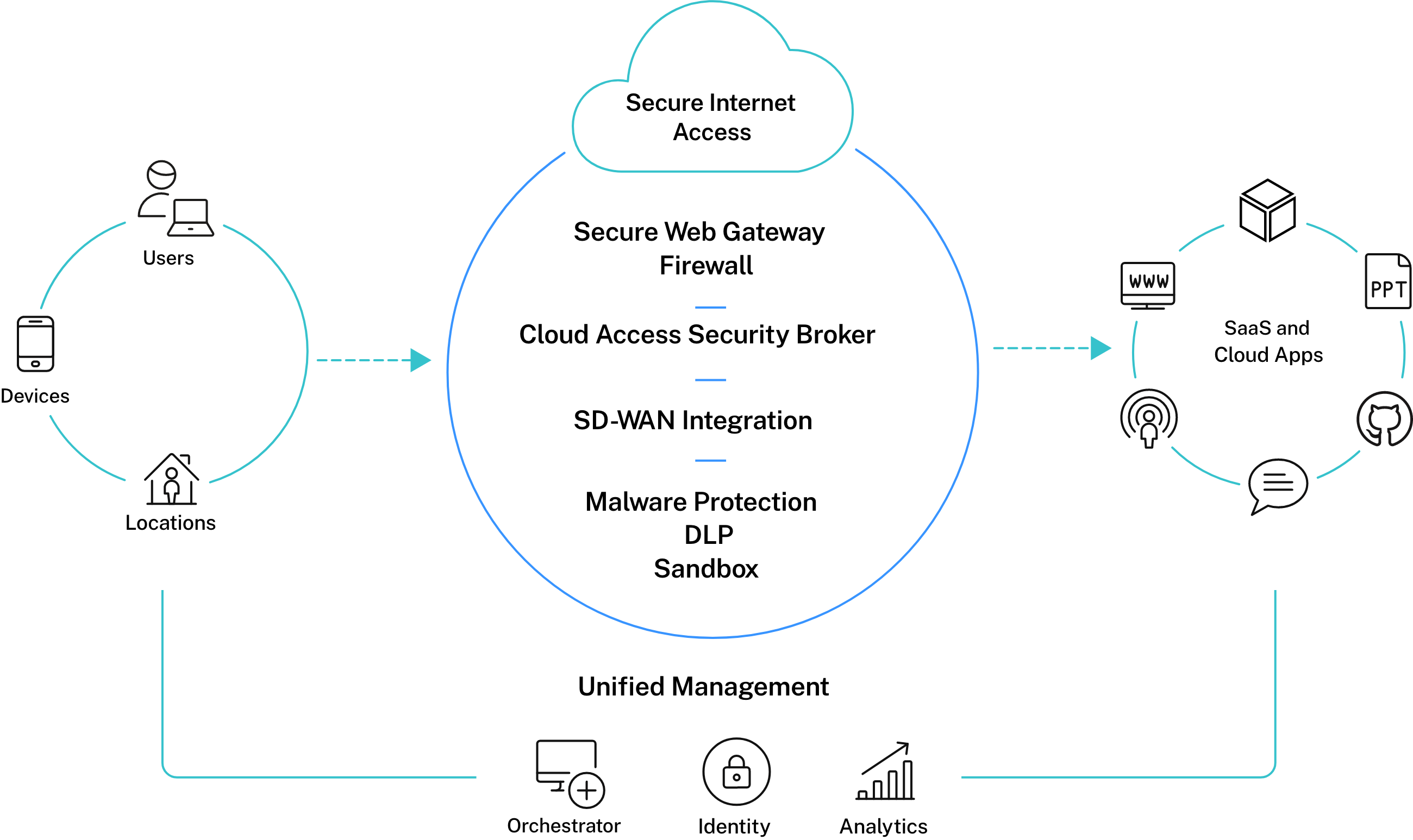
Zero-trust security, as its name suggests, doesn’t grant unconditional trust in users. A zero-trust security system grants access to authorized users based on identity, device, role, and time of ansccess. This approach is different from the traditional “trust but verify” method because it verifies first and trusts later. A zero-trust virtual workspace reduces your attack surface by integrating features like single sign-on (SSO) and multi-factor authentication into a single solution. This significantly reduces the security risks of having a dispersed security stack.
Employees need easy access to web applications and resources, and using a VPN can be problematic when implementing BYOD security. If attackers can bypass the SSL VPN security, they can enter the network and do as they wish.
A contextual network security solution can provide zero-trust functionality while enabling BYOD policies. With an on-premises connector, you can have a single control channel to the company’s environment. Your employees can connect to business web apps without the need for a VPN, improving security and user experience.
How do you prevent attackers from entering a network when the edge changes with new devices and users being added all the time? To manage a distributed workforce or a hybrid environment, IT admin departments must secure everything, everywhere.
By securing internet access with practices like single sign-on to filter out malicious users, companies can give users access to the workspace regardless of the device they are using while keeping security tight. In addition, secure internet access simplifies IT by eliminating multiple password problems or resetting access privileges. Unifying the access through a centralized collaborative workspace provides a seamless user experience for employees.
As more people use their own devices for work, there can be a mix of operating systems and mobile devices connecting to the same workspace. For this reason, it’s important to choose an endpoint security solution that can secure every endpoint and enable management from one console. Using a single console makes it easier to be proactive and prevent threats. When an IT security team doesn’t need to handle dozens of different security tools, they can act quickly to identify threats and sound alerts.
Secure remote access provides a great experience to your employees. An access control solution that employees and stakeholders can use safely will simplify operations and increase productivity. Ensure employees have seamless access to the applications and resources they need even when they move across devices, and improve efficiency with the flexibility to store and access data securely.
Securing access to applications and data means more than protecting your environment against threats and vulnerabilities. Access must also be seamless, without the need for multiple passwords or multiple sign-ins.
With the increase of hybrid workforces, both remote and in-house employees need easy and secure access to applications and data. Companies cannot risk their data over dispersed devices without a central security system.
Citrix offers a complete work-from-anywhere workspace with an advanced zero-trust security approach. In addition, it is VPN-less, which allows workers to access internal web apps and SaaS applications without needing to connect to the network. These secure access solutions ensure your applications and data are protected regardless of where or when the employees work, or which devices they use.