NetScaler API protection provides a range of security features that can protect your applications from malicious attacks. To stop bad actors who seek to exploit vulnerabilities helps you safeguard your APIs against common attacks such as SQL injection, cross-site scripting, and cross-site request forgery.
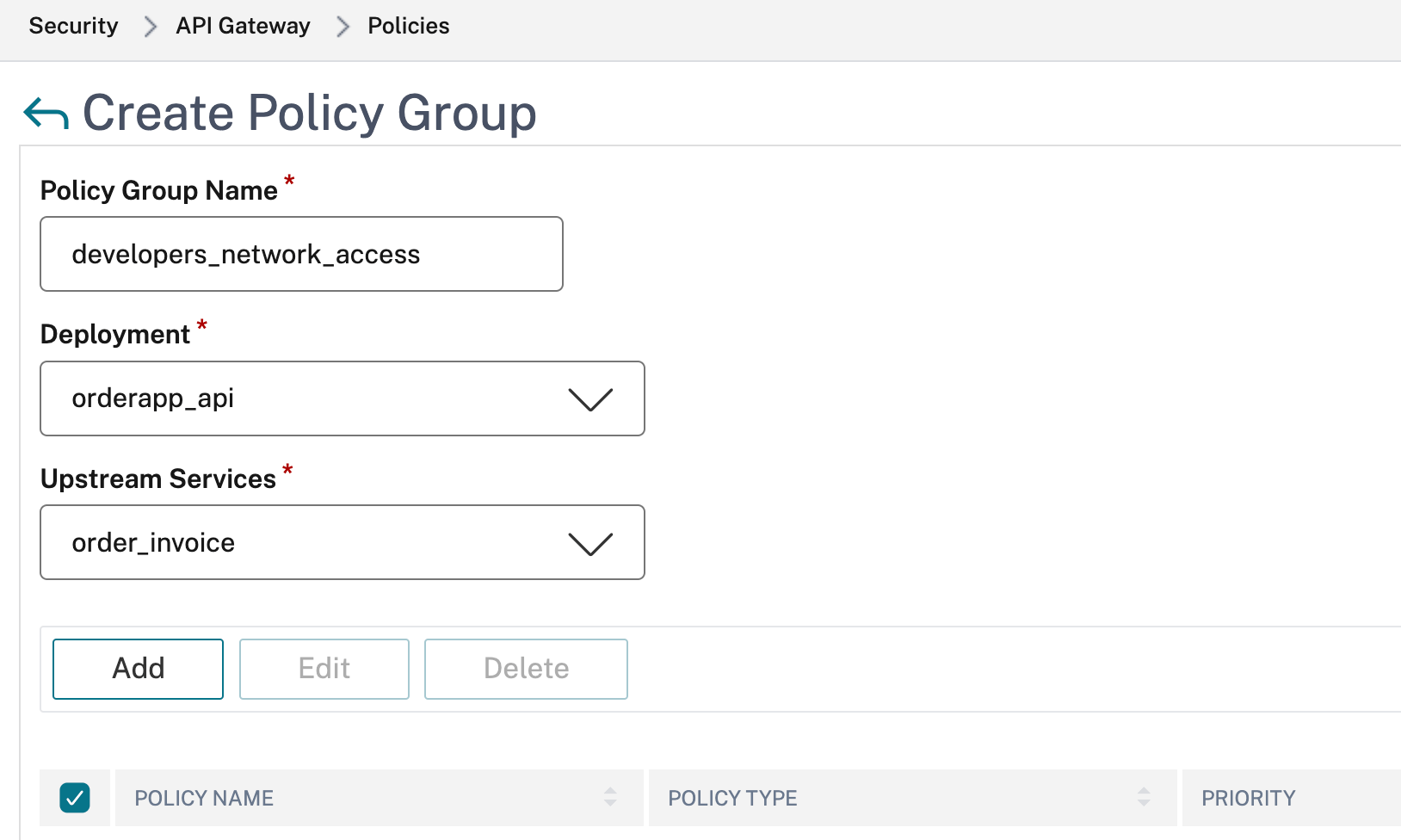
NetScaler API protection also lets you monitor traffic to your APIs and prevent unauthorized access by setting up policies to allow or block traffic based on various criteria such as IP address, user agent, and content type and malicious traffic from reaching their applications.
Another benefit of NetScaler API protection is that it provides you with advanced analytics and reporting capabilities so you can track the performance and use of your APIs, identify potential vulnerabilities and attacks, and take action to remediate them.
KEY CAPABILITIES
What you can do with NetScaler API protection

Secure APIs through encryption, rate limiting, authentication, application firewall protection, and more

Secure your APIs across on-premises and cloud deployments with one dashboard

Ensure that your APIs are always available to minimize application downtime

Gain visibility into API with reports on API traffic volume, daily patterns, API server response time, API client locations, and more

Perform API detection to flag unauthorized APIs and remove or secure them

Benefit from ML-powered detection to identify zero-day attacks and other advanced attacks that aren’t possible to see with static analysis tools like signatures
KEY FEATURE
Securing applications with API protection
NetScaler API protection at a glance
Gateway for single point of entry
NetScaler functions as a gateway to provide a single point of entry for API calls. It performs rate limiting, authentication and authorization, content routing, and additional tasks to ensure secure, reliable access to backend services via your APIs.
ML-based detection to stop advanced attacks
NetScaler uses ML to stop a variety of cyberattacks, including excessive client connections via API and attempted account takeovers. Notably, the NetScaler platform does not place excessive CPU or memory load on NetScaler instances, and its detection capabilities are continuously available, so there’s no need for manual upgrades.
Integrated firewall
Because an API call is an HTTP call over a connection secured by TLS, you can use NetScaler WAF protection on HTTP/XML and JSON-compliant requests and responses for such capabilities as content switching and health checks to alert you to such issues as origin servers going down.
Actionable reporting
Granular analytics and reporting make it easy to detect issues like WAF and bot violations and take immediate action.
Resources
Get started with NetScaler
Request a demo or talk to sales
1-866-NetScaler