The purpose of the blog is to provide a guide on how to decrypt SSL/TLS traffic without a private key.
The purpose of the blog is to provide a guide on how to decrypt SSL/TLS traffic without a private key.
There are many times when IT admins need to utilize a packet inspection such as Wireshark. When the application data is encrypted however, troubleshooting application data becomes more of a challenge. This is especially true with FIPs NetScaler applianes. Normally, the easiest way to decrypt data is to use the private key for the corresponding public key. Wireshark provides another means for decrypting data as well by using the pre-master secret. I will not dive into the intricacies of why this can be used to decrypt data because that part of cryptology is an entirely separate topic. For an in-depth explanation see http://www.moserware.com/2009/06/first-few-milliseconds-of-https.html.
So now let’s dive in. I will use one of our labs from demo.citrix.com to demonstrate how to configure and test decryption using the premaster key.
Step 1.
The first thing you will need to do is configure an environment variable (Windows 7). Right click on My Computer –> Properties –> Advanced System Settings. In the Advanced Tab click Environment Variables.
Step 2.
Under the System variables, click New. You will add the System variable SSLKEYLOGFILE. Create a path from the variable ending with premaster.txt. See the image below for more details.
Step 3.
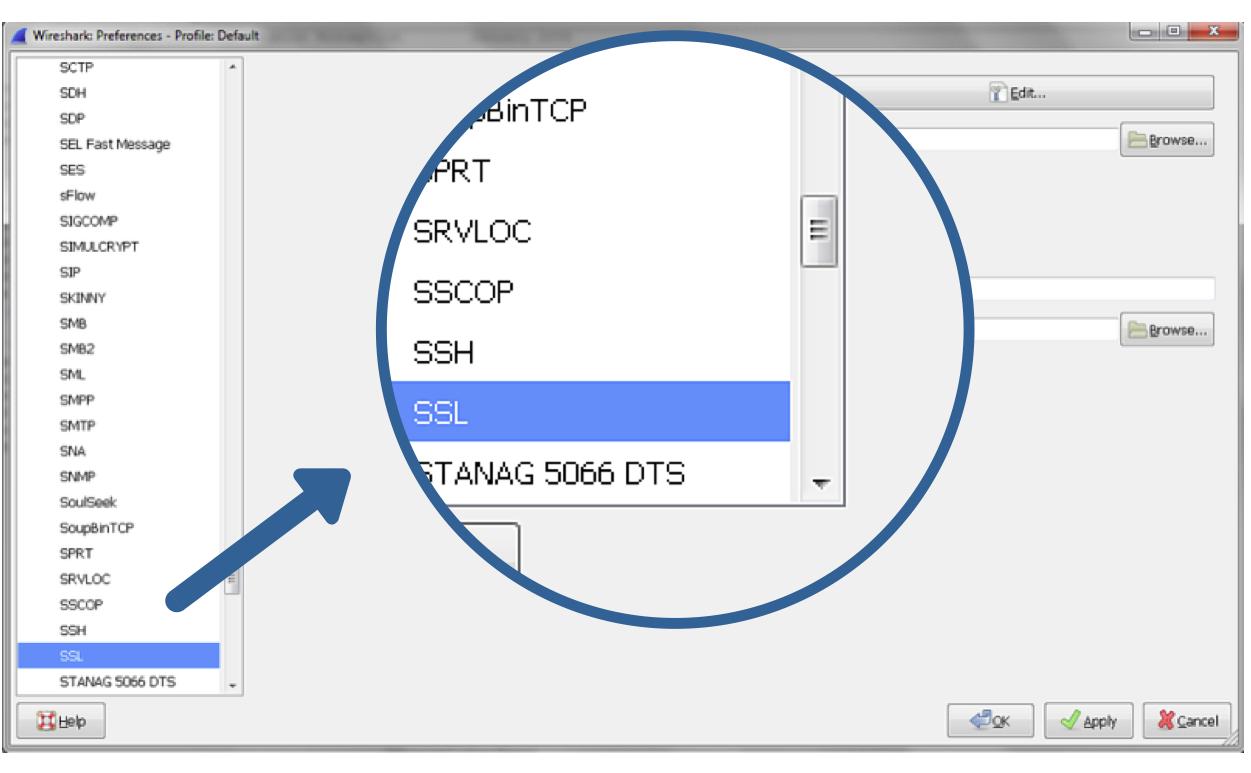
Once this is set, we will point Wireshark to the premaster file by navigating to Edit –> Preferences –> Protocols –>SSL(Pre)-Master-Secret log filename. Click browse and select the premaster.txt file we created earlier. You will need to generate some encrypted traffic via Firefox or Chrome before the file will show up. Internet Explorer will not work for decrypting data using this method.
Step 4.
For the majority of situations encrypted traffic captured by Wireshark while navigating SSL/TLS encrypted sites with Chrome or Firefox will now appear as decrypted. A trace can also be taken from a NetScaler appliance, and then decrypted for a specific client utilizing the SSLKEYLOGFILE Environment Variable. For information on sharing a trace without distributing a private key, please see http://support.citrix.com/article/CTX135889.
I’d like to give special credit to the author of the article below for inspiring this article.
http://www.root9.net/2012/11/ssl-decryption-with-wireshark-private.html
Happy Decrypting! And let me know if you have questions in the comments below.